Pegasus spyware scandal returns to haunt Thai govt

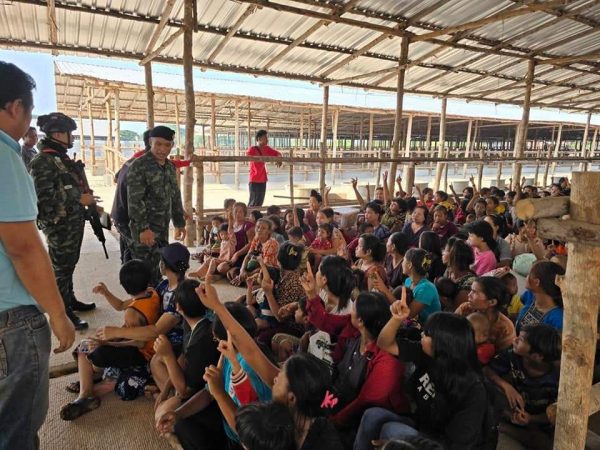
Allegations that Thai authorities used surveillance spyware on government critics returned to haunt those in power just a day before the no-confidence debate started on Tuesday.
It was reported that at least 30 Thai activists, academics and civil society leaders involved in street protests were monitored over the past two years with the Israeli-made Pegasus spyware.
Digital Economy and Society Minister Chaiwut Thanakamanusorn insisted in Parliament on Tuesday that Thai authorities had used surveillance software to track individuals only in “limited” cases involving national security or illicit drugs.
The latest allegation is based on a joint investigation by Thai human rights group iLaw, Southeast Asian internet watchdog Digital Reach, and Canadian cybersecurity watchdog Citizen Lab. The probe uncovered the use of Pegasus spyware on at least 30 government critics between October 2020 to November 2021.
How the spyware works
Last November, concerns over possible state-sponsored cyber-spying were raised after Apple Inc reportedly warned at least six critics of the Thai government that their smartphones were being targeted.
Pegasus spyware has been detected on the phones of critics and opponents of authoritarian governments around the world.
It was first discovered in August 2016 by researchers from Citizen Lab and mobile security firm Lookout. Their investigation revealed that the spyware was designed to infect an iPhone in order to steal all its data, intercept its communications and turn it into a listening device.
By clicking on a phony link from the attacker, the targeted user effectively allows their iPhone to be remotely “jailbroken” — a technical term that means removing software restrictions imposed on iOS and Apple devices. Once the phone is jailbroken, the attacker is able to gain unrestricted access to the targeted iPhone.
After Apple issued a patch to fix the loophole, the spyware evolved to become more effective — able to infect targeted devices without the need for owners to click on a booby-trapped link or message.
Many apps automatically create a cache of preview links in order to improve the user experience, and Pegasus takes advantage of this functionality to silently infect the device. Apple released another patch to fix this loophole in iOS last September.
Thai police deny use of Pegasus spyware against anti-government elements
Maker of notorious spyware
Pegasus is made by the Israeli technology firm NSO Group. Spyware is a powerful hacking tool that is supposedly only available to law enforcement and intelligence agencies to use for legitimate and legal purposes, such as fighting crime.
In November, Apple filed a lawsuit against NSO Group accusing it of surveillance and targeting US Apple users with Pegasus spyware. The iPhone maker is also seeking to ban the Israeli cyber firm from using any Apple software, services or devices to prevent further abuse.
The United States government blacklisted NSO for actions “contrary to the foreign policy and national security interests of the US”.
The spyware creator is also facing legal action or criticism from other global tech companies, including Microsoft Corp, Meta Platforms Inc (owner of Facebook, WhatsApp, and Instagram), Alphabet Inc (Google), and Cisco Systems Inc.
WhatsApp claims that senior state officials, journalists, human rights defenders, and activists were among 1,400 individuals targeted by governments using the NSO spyware in 2019.
In April 2019, NSO suspended its business with Saudi Arabia following allegations that Pegasus was used to track journalist Jamal Khashoggi in the months before he was assassinated at the Saudi consulate in Istanbul.
NSO Group denied any wrongdoing, saying its products have been used by governments across the world to save lives threatened by tech-savvy criminals.
Thailand among the customers
Citizen Lab found that Thailand was likely among customers of Circles, an affiliate of NSO Group that reportedly exploits weaknesses in the global mobile phone system to snoop on calls, texts, and the location of phones around the globe.
By using Internet scanning, Citizen Lab identified Circles deployments in at least 25 countries, including Thailand, according to its 2020 research report “Running in Circles: Uncovering the Clients of Cyberespionage Firm Circles”.
Other suspected customers range from developed nations like Australia, Belgium, and Denmark to developing countries like Vietnam, Zambia, and Zimbabwe.
The report named three Thai state agencies as likely customers of the surveillance firm — the Internal Security Operations Command (ISOC), Military Intelligence Battalion, and Narcotics Suppression Bureau.
By Thai PBS World’s Political Desk